strComputer = "."
DriveLetter = ""
Set objWMIService = GetObject("winmgmts:\\" & strComputer & "\root\cimv2")
Set colItems = objWMIService.ExecQuery ("Select * From Win32_LogicalDisk")
For Each objItem in colItems
If objItem.VolumeName = "KINGSTON" then DriveLetter = objItem.DeviceID
Next
msgbox DriveLetter
Office 2016 – Disable the First things first Window
When launching one of the Office apps on first login, the user will receive a First things first window. To disable this window, apply the reg keys below.
Screenshot
Single User Method
[HKEY_CURRENT_USER\SOFTWARE\Policies\Microsoft\Office\16.0\Common\General]
“OptInDisable”=dword:00000001
[HKEY_CURRENT_USER\SOFTWARE\Policies\Microsoft\Office\16.0\Registration]
“AcceptAllEulas”=dword:00000001
* Note, you may need RW permissions to the Microsoft key…if you do, add Authenticated Users with RW permissions.
Default User Profile Method
REG LOAD HKLM\DEFAULT C:\Users\Default\ntuser.dat
REG ADD “HKLM\DEFAULT\SOFTWARE\Policies\Microsoft\Office\16.0\Common\General” /v “OptInDisable” /t REG_DWORD /d 1 /f /REG:64
REG ADD “HKLM\DEFAULT\SOFTWARE\Policies\Microsoft\Office\16.0\Registration” /v “AcceptAllEulas” /t REG_DWORD /d 1 /f /REG:64
REG UNLOAD HKLM\DEFAULT
Or, if you’re really crafty, launch this as admin when the user logs in
on error resume next
Set objShell = CreateObject("Wscript.Shell")
Const HKEY_LOCAL_MACHINE = &H80000002
Const OverwriteExisting = TRUE
'SETS CURRENT DIRECTORY TO VARIABLE
strCurrentDirectory = objShell.CurrentDirectory
'SETS COMPUTER NAME
strComputer = "."
'SET UP WMI
Set objWMIService = GetObject("winmgmts:\\" & strComputer & "\root\cimv2")
'SET UP REGISTRY
Set objRegistry = GetObject("winmgmts:\\" & strComputer & "\root\default:StdRegProv")
strKeyPath = "SOFTWARE\Wow6432Node\Microsoft\Windows NT\CurrentVersion\ProfileList"
objRegistry.EnumKey HKEY_LOCAL_MACHINE, strKeyPath, arrSubkeys
For Each objSubkey In arrSubkeys
on error resume next
strValueName = "ProfileImagePath"
strSubPath = strKeyPath & "\" & objSubkey
objRegistry.GetExpandedStringValue HKEY_LOCAL_MACHINE,strSubPath,strValueName,strValue
Const POPUP_TITLE = "User To SID Conversion"
Set objWMIService = GetObject("winmgmts:\\" & strComputer & "\root\cimv2")
Set objAccount = objWMIService.Get("Win32_SID.SID='" & objSubkey & "'")
strUser = objAccount.AccountName
'strDomain = objAccount.ReferencedDomainName'returns referenced domain
'PROFILE NAME & SID
objSubkey = trim(objSubkey)'trims whitespace
strUser = trim(strUser)'trims whitespace
'LOGIC TO DETERMINE IF REGISTRY ACCOUNT IS TO BE ACCESSED
if strUser = "SYSTEM" then strUser = ""
if strUser = "LOCAL SERVICE" then strUser = ""
if strUser = "NETWORK SERVICE" then strUser = ""
'if strUser = "Administrator" then strUser = ""
if strUser = "Default" then strUser = ""
if strUser <> "" then
on error resume next
'APPLY REG KEYS
objShell.Run "%comspec% /c reg.exe add "&chr(34)&"HKEY_USERS\" & objSubkey & "\SOFTWARE\Policies\Microsoft\Office\16.0\Common\General"&chr(34)&" /t REG_DWORD /v ""OptInDisable"" /d 1 /f",0,true
objShell.Run "%comspec% /c reg.exe add "&chr(34)&"HKEY_USERS\" & objSubkey & "\SOFTWARE\Policies\Microsoft\Office\16.0\Registration"&chr(34)&" /t REG_DWORD /v ""AcceptAllEulas"" /d 1 /f",0,true
Wscript.Sleep 1000
end if
Next
Notes
SCCM – Imaging, Join Domain Fails in Task Sequence
If you have computers that aren’t joining the domain during the task sequence, and you receive the following errors in the C:\Windows\debug\NetSetup.log file, the cause is most likely the rights on the service account used on the Join Domain/Apply Network Settings item in the task sequence.
NetpMapGetLdapExtendedError: Parsed [0x5] from server extended error string: 00000005: SecErr: DSID-031A11CC, problem 4003 (INSUFF_ACCESS_RIGHTS), data 0
NetpModifyComputerObjectInDs: ldap_modify_s failed: 0x32 0x5
NetpCreateComputerObjectInDs: NetpModifyComputerObjectInDs failed: 0x5
NetpProvisionComputerAccount: LDAP creation failed: 0x5
To fix this, you need to modify the service account delegation rights. In ADUC:
- Identify the security principal that you want to delegate permissions for.
- Identify the container or OU where you want to allow users to manipulate computer objects.
- Right click the container or OU and choose Delegate Control.
- The Delegation of Control Wizard opens, click Next.
- The Users or Groups window opens:
Select the security principal you want to grant permissions to, and then click Next again. - The Tasks to Delegate window opens:
Select Create a custom task to delegate and click Next. - The Active Directory Object Type window opens:
Select Only the following objects in the folder and then select Computer objects. At the bottom of the window, select Create selected objects in this folder and Delete selected objects in this folder, and click Next. - The Permissions window opens
Select General and Property-specific options, and then select these permissions:
– Read All Properties
– Write All Properties
– Reset Password
– Read and write Account Restrictions
– Validated write to DNS host name
– Validated write to service principal name - The Completing the Delegation of Control Wizard window will open showing you a summary of the actions. Click Finish.
Test your imaging process now.
Notes
Windows – UserAccountControl Attribute
UserAccountControl Attribute/Flag Values
Searching Active Directory attributes using DSQUERY commands or scripts is not difficult. You can acquire the values directly from the attribute. However, searching the statuses for enabled, disabled, PasswordExpired, etc., can be challenging because these properties and values are not stored in their own attributes. These account properties are controlled by an attribute called userAccountControl.
UserAccountControl is a 4 bytes (32-bit) integer that represents a bitwise enumeration of various flags—these flags control the behavior of objects. The attributeID (ruleOD) of this object is 1.2.840.113556.1.4.8. The attributeID is a unique X.500 Object Identifier(OID) for identifying an attribute.
How do I search userAccountControl values in Active Directory?
It is like searching any other attribute in Active Directory. However, you need to represent the userAccountControl values in numeric. The syntax of the LDAP matching rule is
attributename:ruleOID:=value
…where attributename is the LDAP DisplayName -in this case it is userAccountControl, ruleOID is the attributeID for the matching rule control – in this case it is 1.2.840.113556.1.4.80X, and value is the decimal value you want to use for search.
The following DSQUERY command returns all disabled user accounts in Active Directory.
dsquery * -limit 0 –filter “(&(objectCategory=person)(objectClass=user)(userAccountControl:1.2.840.113556.1.4.803:=2))” –attr name
userAccountControl =2 means the user account is disabled (ADS_UF_ACCOUNTDISABLE)
and the following DSQUERY command returns all users with the ‘Password Never Expires’ settings enabled.
dsquery * -limit 0 –filter “(&(objectCategory=person)(objectClass=user)(userAccountControl:1.2.840.113556.1.4.803:=65536))” –attr name
userAccountControl =65536 means the user account has ‘Password Never Expires’ flag enabled (ADS_UF_DONT_EXPIRE_PASSWD)
———————————–
Note
The UserAccountControl =XXXXX portion will be what you look up in the attribute table (see below).
———————————–
Where did the 1.2.840.113556.1.4.803 attributeID (ruleOID) come from?
The value of attributeID (ruleOID) can be either bitwise AND (1.2.840.113556.1.4.803) or bitwise OR (1.2.840.113556.1.4.804)
1.2.840.113556.1.4.803 – This is the bitwise AND operator (LDAP_MATCHING_RULE_BIT_AND). The rule is true only if all bits from the property match the value.
1.2.840.113556.1.4.804 – This is the bitwise OR operator (LDAP_MATCHING_RULE_BIT_OR). The rule is true if any bits from the property match the value.
Attribute Table
A comprehensive list of UserAccountrControl attribute/flag values
| Property Flag | Value In Hexadecimal | Value In Decimal | Not Officially Documented |
| SCRIPT | 0x0001 | 1 | |
| ACCOUNTDISABLE | 0x0002 | 2 | |
| HOMEDIR_REQUIRED | 0x0008 | 8 | |
| LOCKOUT | 0x0010 | 16 | |
| PASSWD_NOTREQD | 0x0020 | 32 | |
| PASSWD_CANT_CHANGE | 0x0040 | 64 | |
| ENCRYPTED_TEXT_PWD_ALLOWED | 0x0080 | 128 | |
| TEMP_DUPLICATE_ACCOUNT | 0x0100 | 256 | |
| NORMAL_ACCOUNT | 0x0200 | 512 | |
| Disabled Account | 0x0202 | 514 | x |
| Enabled, Password Not Required | 0x0220 | 544 | x |
| Disabled, Password Not Required | 0x0222 | 546 | x |
| INTERDOMAIN_TRUST_ACCOUNT | 0x0800 | 2048 | |
| WORKSTATION_TRUST_ACCOUNT | 0x1000 | 4096 | |
| SERVER_TRUST_ACCOUNT | 0x2000 | 8192 | |
| DONT_EXPIRE_PASSWORD | 0x10000 | 65536 | |
| Enabled, Password Doesn’t Expire | 0x10200 | 66048 | x |
| Disabled, Password Doesn’t Expire | 0x10202 | 66050 | x |
| Disabled, Password Doesn’t Expire & Not Required | 0x10222 | 66082 | x |
| MNS_LOGON_ACCOUNT | 0x20000 | 131072 | |
| SMARTCARD_REQUIRED | 0x40000 | 262144 | |
| Enabled, Smartcard Required | 0x40200 | 262656 | x |
| Disabled, Smartcard Required | 0x40202 | 262658 | x |
| Disabled, Smartcard Required, Password Not Required | 0x40222 | 262690 | x |
| Disabled, Smartcard Required, Password Doesn’t Expire | 0x50202 | 328194 | x |
| Disabled, Smartcard Required, Password Doesn’t Expire & Not Required | 0x50222 | 328226 | x |
| TRUSTED_FOR_DELEGATION | 0x80000 | 524288 | |
| Domain controller | 0x82000 | 532480 | |
| NOT_DELEGATED | 0x100000 | 1048576 | |
| USE_DES_KEY_ONLY | 0x200000 | 2097152 | |
| DONT_REQ_PREAUTH | 0x400000 | 4194304 | |
| PASSWORD_EXPIRED | 0x800000 | 8388608 | |
| TRUSTED_TO_AUTH_FOR_DELEGATION | 0x1000000 | 16777216 | |
| PARTIAL_SECRETS_ACCOUNT | 0x04000000 | 67108864 |
Notes
Property flag descriptions
- SCRIPT – The logon script will be run.
- ACCOUNTDISABLE – The user account is disabled.
- HOMEDIR_REQUIRED – The home folder is required.
- PASSWD_NOTREQD – No password is required.
- PASSWD_CANT_CHANGE – The user cannot change the password. This is a permission on the user’s object. For information about how to programmatically set this permission, visit the following Web site:
- ENCRYPTED_TEXT_PASSWORD_ALLOWED – The user can send an encrypted password.
- TEMP_DUPLICATE_ACCOUNT – This is an account for users whose primary account is in another domain. This account provides user access to this domain, but not to any domain that trusts this domain. This is sometimes referred to as a local user account.
- NORMAL_ACCOUNT – This is a default account type that represents a typical user.
- INTERDOMAIN_TRUST_ACCOUNT – This is a permit to trust an account for a system domain that trusts other domains.
- WORKSTATION_TRUST_ACCOUNT – This is a computer account for a computer that is running Microsoft Windows NT 4.0 Workstation, Microsoft Windows NT 4.0 Server, Microsoft Windows 2000 Professional, or Windows 2000 Server and is a member of this domain.
- SERVER_TRUST_ACCOUNT – This is a computer account for a domain controller that is a member of this domain.
- DONT_EXPIRE_PASSWD – Represents the password, which should never expire on the account.
- MNS_LOGON_ACCOUNT – This is an MNS logon account.
- SMARTCARD_REQUIRED – When this flag is set, it forces the user to log on by using a smart card.
- TRUSTED_FOR_DELEGATION – When this flag is set, the service account (the user or computer account) under which a service runs is trusted for Kerberos delegation. Any such service can impersonate a client requesting the service. To enable a service for Kerberos delegation, you must set this flag on the userAccountControl property of the service account.
- NOT_DELEGATED – When this flag is set, the security context of the user is not delegated to a service even if the service account is set as trusted for Kerberos delegation.
- USE_DES_KEY_ONLY – (Windows 2000/Windows Server 2003) Restrict this principal to use only Data Encryption Standard (DES) encryption types for keys.
- DONT_REQUIRE_PREAUTH – (Windows 2000/Windows Server 2003) This account does not require Kerberos pre-authentication for logging on.
- PASSWORD_EXPIRED – (Windows 2000/Windows Server 2003) The user’s password has expired.
- TRUSTED_TO_AUTH_FOR_DELEGATION – (Windows 2000/Windows Server 2003) The account is enabled for delegation. This is a security-sensitive setting. Accounts that have this option enabled should be tightly controlled. This setting lets a service that runs under the account assume a client’s identity and authenticate as that user to other remote servers on the network.
- PARTIAL_SECRETS_ACCOUNT – (Windows Server 2008/Windows Server 2008 R2) The account is a read-only domain controller (RODC). This is a security-sensitive setting. Removing this setting from an RODC compromises security on that server.
UserAccountControl values
These are the default UserAccountControl values for the certain objects:
- Typical user : 0x200 (512)
- Domain controller : 0x82000 (532480)
- Workstation/server: 0x1000 (4096)
To set or erase bits in the userAccountControl attribute
Const ADS_UF_ACCOUNT_DISABLE = 2
Const ADS_UF_HOMEDIR_REQUIRED = 8
Const ADS_UF_LOCKOUT = 16
Const ADS_UF_PASSWD_NOTREQD = 32
Const ADS_UF_PASSWD_CANT_CHANGE = 64
Const ADS_UF_ENCRYPTED_TEXT_PASSWORD_ALLOWED = 128
Const ADS_UF_NORMAL_ACCOUNT = 512
Const ADS_UF_INTERDOMAIN_TRUST_ACCOUNT = 2048
Const ADS_UF_WORKSTATION_TRUST_ACCOUNT = 4096
Const ADS_UF_SERVER_TRUST_ACCOUNT = 8192
Const ADS_UF_DONT_EXPIRE_PASSWD = 65536
Const ADS_UF_MNS_LOGON_ACCOUNT = 131072
Const ADS_UF_SMARTCARD_REQUIRED = 262144
Const ADS_UF_TRUSTED_FOR_DELEGATION = 524288
Const ADS_UF_NOT_DELEGATED = 1048576
Const ADS_UF_USE_DES_KEY_ONLY = 2097152
Const ADS_UF_DONT_REQUIRE_PREAUTH = 4194304
Const ADS_UF_PASSWORD_EXPIRED = 8388608
Const ADS_UF_TRUSTED_TO_AUTHENTICATE_FOR_DELEGATION = 16777216
Const ADS_UF_NO_AUTH_DATA_REQUIRED = 33554432
Const ADS_UF_PARTIAL_SECRETS_ACCOUNT = 67108864
Set obj = GetObject("LDAP://cn=site,ou=user,dc=contoso,dc=com")
'The user is disabled (set flag bit):
obj.userAccountControl = obj.userAccountControl or ADS_UF_ACCOUNT_DISABLE
obj.SetInfo
'The user is enabled (remove flag bit):
obj.userAccountControl = obj.userAccountControl xor ADS_UF_ACCOUNT_DISABLE
obj.SetInfo
Reference
User-Account-Control attribute
How to use the UserAccountControl flags to manipulate user account properties
Windows 10 – Useful Registry Paths for Apps & Settings
Note, these may change from build version to build version. Make sure you’re using the correct Name and/or App ID.
Cortana displays history
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\HistoryViewEnabled
Type: REG_DWORD, Length: 4, Data: 0
Cortana can use my device history
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\DeviceHistoryEnabled
Type: REG_DWORD, Length: 4, Data: 0
Disable Location
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{BFA794E4-F964-4FDB-90F6-51056BFE4B44}\Value
Type: REG_SZ, Length: 10, Data: Deny
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{E6AD100E-5F4E-44CD-BE0F-2265D88D14F5}\Value
Type: REG_SZ, Length: 10, Data: Deny
HKCU\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Sensor\Permissions\{BFA794E4-F964-4FDB-90F6-51056BFE4B44}\SensorPermissionState
Type: REG_DWORD, Length: 4, Data: 0
Advertising ID
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\AdvertisingInfo\Enabled
Type: REG_DWORD, Length: 4, Data: 0
Smartscreen
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\AppHost\EnableWebContentEvaluation
Type: REG_DWORD, Length: 4, Data: 0
Send typing info to Microsoft
HKCU\SOFTWARE\Microsoft\Input\TIPC\Enabled
Type: REG_DWORD, Length: 4, Data: 0
Let websites provide local content by accessing language list
HKCU\SOFTWARE\Microsoft\Internet Explorer\International\AcceptLanguage
Type: REG_SZ, Length: 30, Data: en-US,en;q=0.5
HKCU\Control Panel\International\User Profile\HttpAcceptLanguageOptOut
Type: REG_DWORD, Length: 4, Data: 1
Smartglass; let apps on other devices open apps on this device
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\SmartGlass\UserAuthPolicy
Type: REG_DWORD, Length: 4, Data: 0
Let apps use camera
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{E5323777-F976-4f5b-9B55-B94699C46E44}\Value
Type: REG_SZ, Length: 10, Data: Deny
Let apps use Mic
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{2EEF81BE-33FA-4800-9670-1CD474972C3F}\Value
Type: REG_SZ, Length: 10, Data: Deny
Let apps access notifications
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{52079E78-A92B-413F-B213-E8FE35712E72}\Value
Type: REG_SZ, Length: 10, Data: Deny
Get to know my typing
HKCU\SOFTWARE\Microsoft\Personalization\Settings\AcceptedPrivacyPolicy
Type: REG_DWORD, Length: 4, Data: 0
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\SettingSync\Groups\Language\Enabled
Type: REG_DWORD, Length: 4, Data: 0
HKCU\SOFTWARE\Microsoft\InputPersonalization\RestrictImplicitTextCollection
Type: REG_DWORD, Length: 4, Data: 1
HKCU\SOFTWARE\Microsoft\InputPersonalization\RestrictImplicitInkCollection
Type: REG_DWORD, Length: 4, Data: 1
HKCU\SOFTWARE\Microsoft\InputPersonalization\TrainedDataStore\HarvestContacts
Type: REG_DWORD, Length: 4, Data: 0
Let apps access my account info
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{C1D23ACC-752B-43E5-8448-8D0E519CD6D6}\Value
Type: REG_SZ, Length: 10, Data: Deny
Let apps access my contacts
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{7D7E8402-7C54-4821-A34E-AEEFD62DED93}\Value
Type: REG_SZ, Length: 10, Data: Deny
Let apps access my calendar
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{D89823BA-7180-4B81-B50C-7E471E6121A3}\Value
Type: REG_SZ, Length: 10, Data: Deny
Let apps access my call history
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{8BC668CF-7728-45BD-93F8-CF2B3B41D7AB}\Value
Type: REG_SZ, Length: 10, Data: Deny
Let apps access my email
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{9231CB4C-BF57-4AF3-8C55-FDA7BFCC04C5}\Value
Type: REG_SZ, Length: 10, Data: Deny
Let apps access text/mms
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{992AFA70-6F47-4148-B3E9-3003349C1548}\Value
Type: REG_SZ, Length: 10, Data: Deny
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{21157C1F-2651-4CC1-90CA-1F28B02263F6}\Value
Type: REG_SZ, Length: 10, Data: Deny
Let apps access radios
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{A8804298-2D5F-42E3-9531-9C8C39EB29CE}\Value
Type: REG_SZ, Length: 10, Data: Deny
Let apps share and sync non-explicitly paired wireless devices over uPnP
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\LooselyCoupled\Value
Type: REG_SZ, Length: 10, Data: Deny
Set telemetry to basic (can disable via service Diagtrack and DmwApPushSvc)
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\DataCollection\AllowTelemetry
Type: REG_DWORD, Length: 4, Data: 1
Never ask for feedback
HKCU\SOFTWARE\Microsoft\Siuf\Rules\NumberOfSIUFInPeriod
Type: REG_DWORD, Length: 4, Data: 0
Use my sign in info to automatically finish setting up after an update
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\ARSOUserConsent
Type: REG_DWORD, Length: 4, Data: 2
Delivery optimization, disabled
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\DeliveryOptimization\SystemSettingsDownloadMode
Type: REG_DWORD, Length: 4, Data: 3
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\DeliveryOptimization\Config\DODownloadMode
Type: REG_DWORD, Length: 4, Data: 0
Disable cloud Defender protection (love the key name)
HKLM\SOFTWARE\Microsoft\Windows Defender\Spynet\SpyNetReporting
Type: REG_DWORD, Length: 4, Data: 2
Services:
DiagTrack and Dmwappushsvc – Parts of telemetry
DoSvc – Delivery “optimization”
DcpSvc – Allows first party apps to upload data to the cloud (Data collection and publishing)
lfsvc – Geolocation
XblAuthManager, XblGameSave, XboxNetApiSvc – xBox services
Windows 10 – Set Default Lock Screen Wallpaper – Image
Personalization
reg add “HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\Personalization” /v “LockScreenImage” /t REG_SZ /d “C:\Windows\BackgroundDefault.jpg” /f
or via CSP
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP]
“LockScreenImageStatus”=dword:00000001
“LockScreenImagePath”=”C:\\Windows\\wallpaper.png”
“LockScreenImageUrl”=”C:\\Windows\\wallpaper.png”
Windows 10 – Disable Screen Rotation
Use this reg key to disable the rotation feature
reg add “HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\AutoRotation” /v “SensorPresent” /t REG_DWORD /d 0 /f
Set option to off
reg add “HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\AutoRotation” /v “Enable” /t REG_DWORD /d 0 /f
Notes
SlateEnable = 0
Windows 10 – Auto-Tuning Disable it or not?
Window Auto-Tuning feature is said to improve the performance for programs that receive TCP data over a network. It is nothing new. It was introduced in Windows Vista and is present in Windows 10 too. In today’s Internet, the range of latencies & throughput speeds is just too large to manage statically. It needs to be adjusted dynamically. Windows 10 will dynamically adjust the receive buffer size to the throughput and latency of the link, using this feature.
Programs like Automatic Updates, Windows Update, Remote Desktop Connection, Windows Explorer for network file copy, etc, use WinHTTP or Windows HTTP Services.
Window Auto-Tuning feature is enabled by default in Windows 10 and makes data transfers over networks more efficient. But if your network uses an old router or your firewall software does not support this feature, then you may experience slow data transfers or even loss of connectivity.
To check the status of Auto-Tuning feature on your system, in an elevated command prompt windows, type the following and hit Enter:
netsh interface tcp show global
If you see ‘normal’ written against Receive Window Auto-Tuning Level, it means that the feature is enabled and it is working fine.
To disable Windows AutoTuning, run the following command:
netsh int tcp set global autotuninglevel=disabled
To enable Windows AutoTuning, run the following command:
netsh int tcp set global autotuninglevel=normal
You can also tweak the Windows Registry, says KB947239. To enable the Receive Window Auto-Tuning feature for HTTP traffic, Run regedit and navigate to the following registry subkey:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Internet Settings\WinHttp
Right-click on it > New > DWORD Value. Type TcpAutotuning and give it a vale of 1.
Click OK and exit.
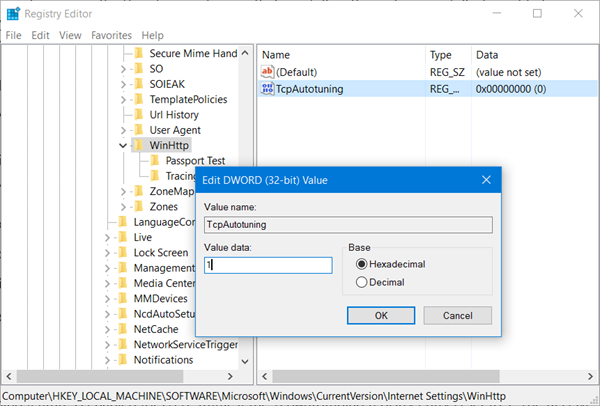
To disable Receive Window Auto-Tuning feature for HTTP traffic, give it a value of 0 or delete the created TcpAutotuning DWORD.
The Receive Window Auto-Tuning feature lets the operating system continually monitor routing conditions such as bandwidth, network delay, and application delay. Therefore, the operating system can configure connections by scaling the TCP receive window to maximize the network performance. To determine the optimal receive window size, the Receive Window Auto-Tuning feature measures the products that delay bandwidth and the application retrieve rates. Then, the Receive Window Auto-Tuning feature adapts the receive window size of the ongoing transmission to take advantage of any unused bandwidth.
Let the default settings of Window Auto-Tuning feature be enabled. If your network uses an old router or your firewall software does not support this feature, and you are experiencing poor or no connectivity issues, only then may you disable this feature and see if it works in your favor.
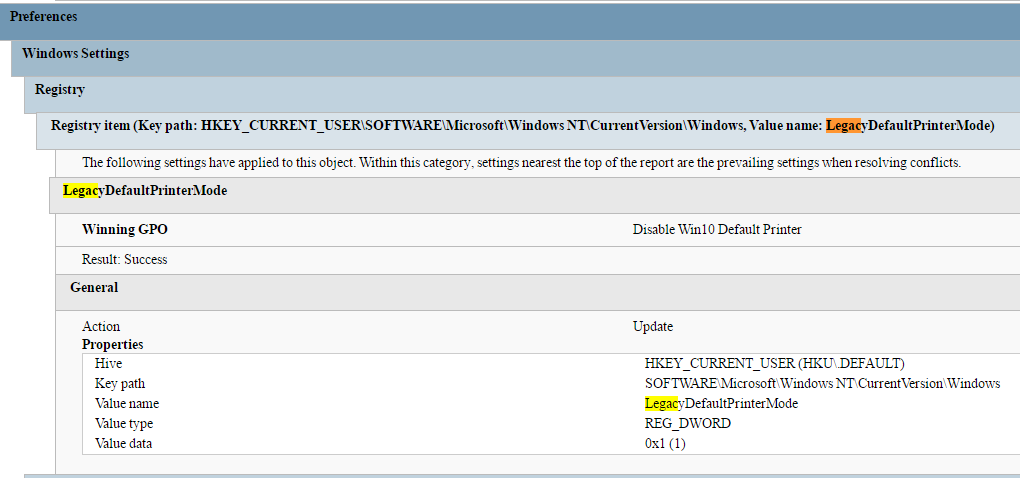
Windows 10 – Default Printer Not Available
This is how you restore the Default printer or Legacy printer setting (these uncheck “Let Windows manage my default printer”):
Registry
REG ADD “HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows” /v “LegacyDefaultPrinterMode” /t REG_DWORD /d 1 /f
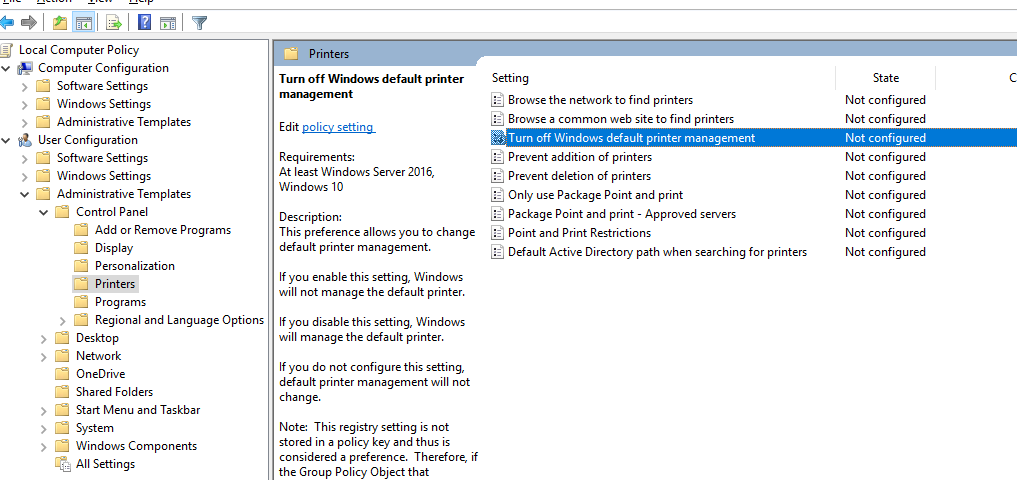
Group Policy
Enable “Turn off Windows default printer management”
User Configuration > Administrative Templates > Control Panel > Printers
Notes
Step-By-Step: Managing Windows 10 with Administrative templates